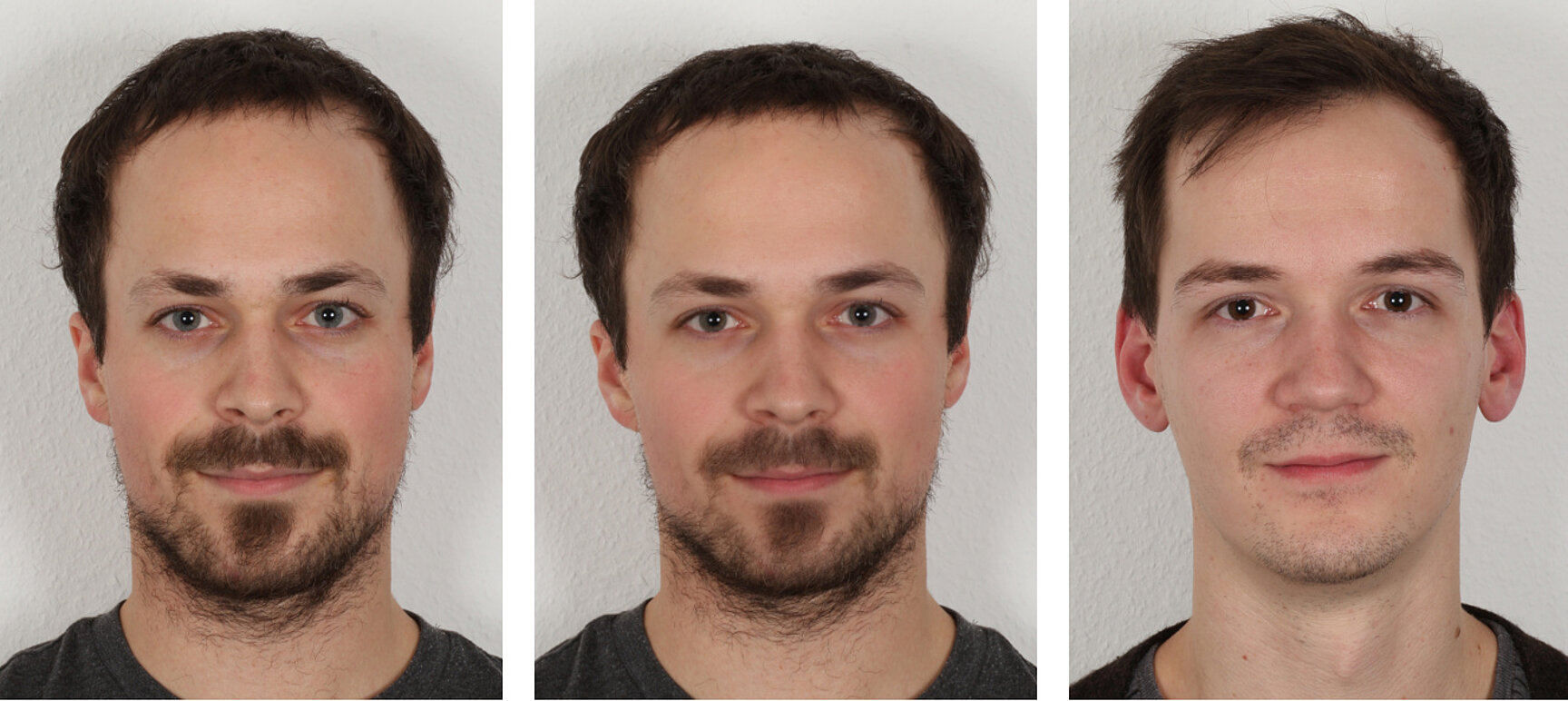
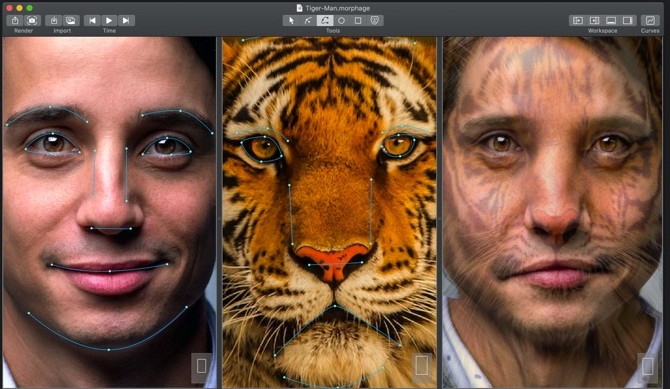
Face morphing attacks: Investigating detection with humans and computers | Cognitive Research: Principles and Implications | Full Text

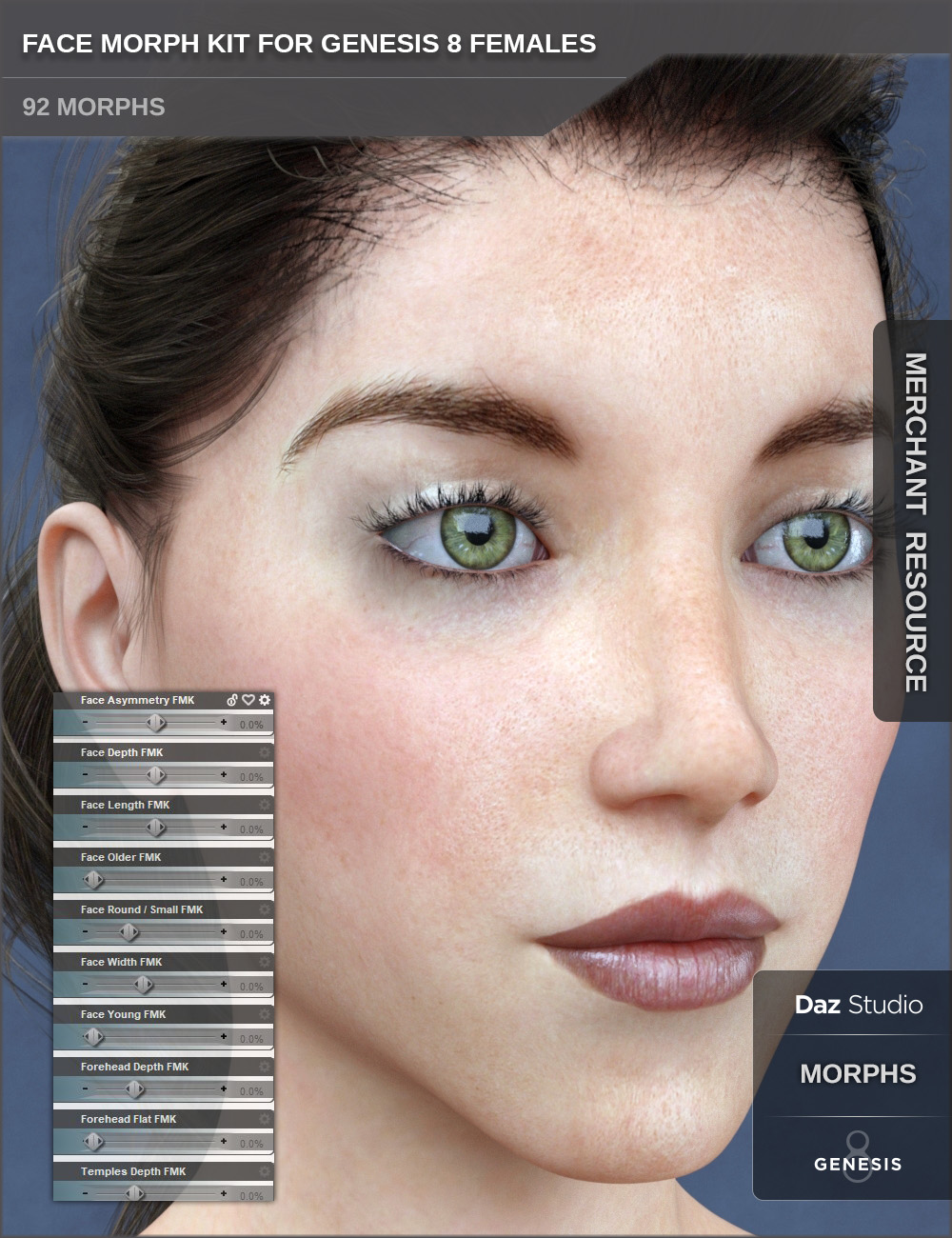
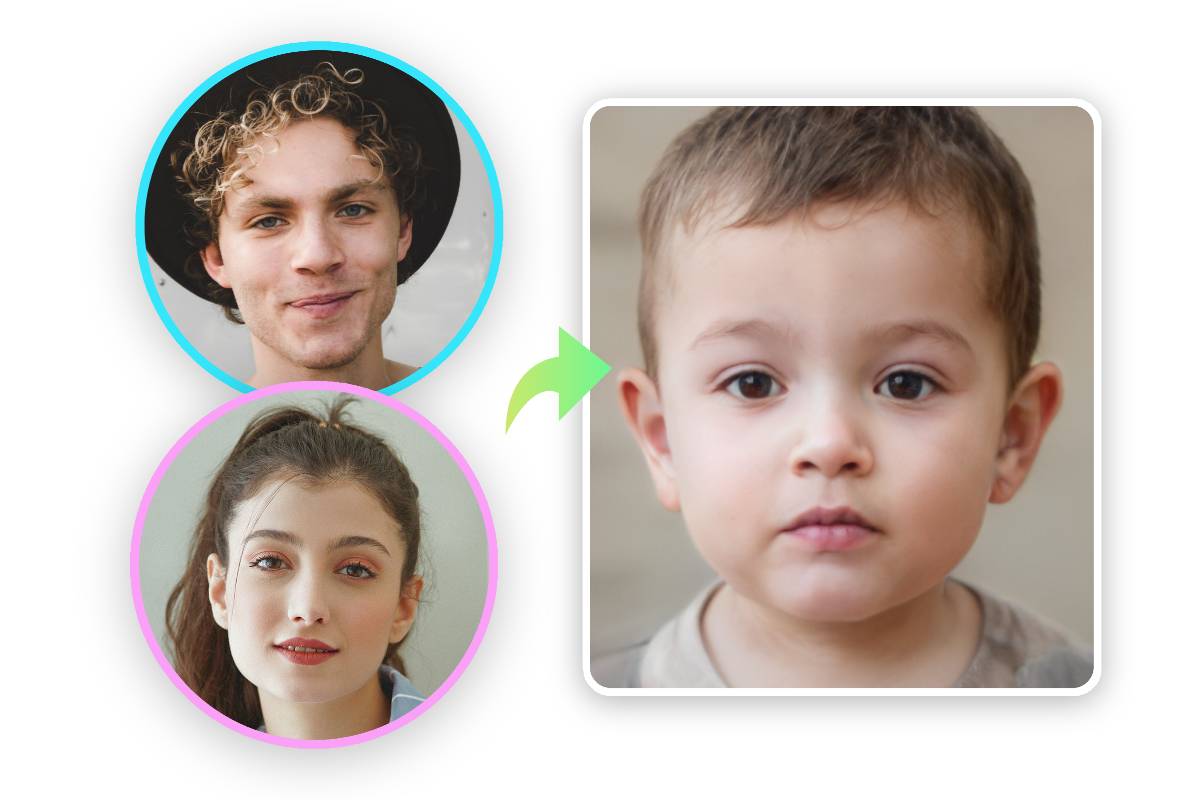
Applied Sciences | Free Full-Text | A Comprehensive Review of Face Morph Generation and Detection of Fraudulent Identities
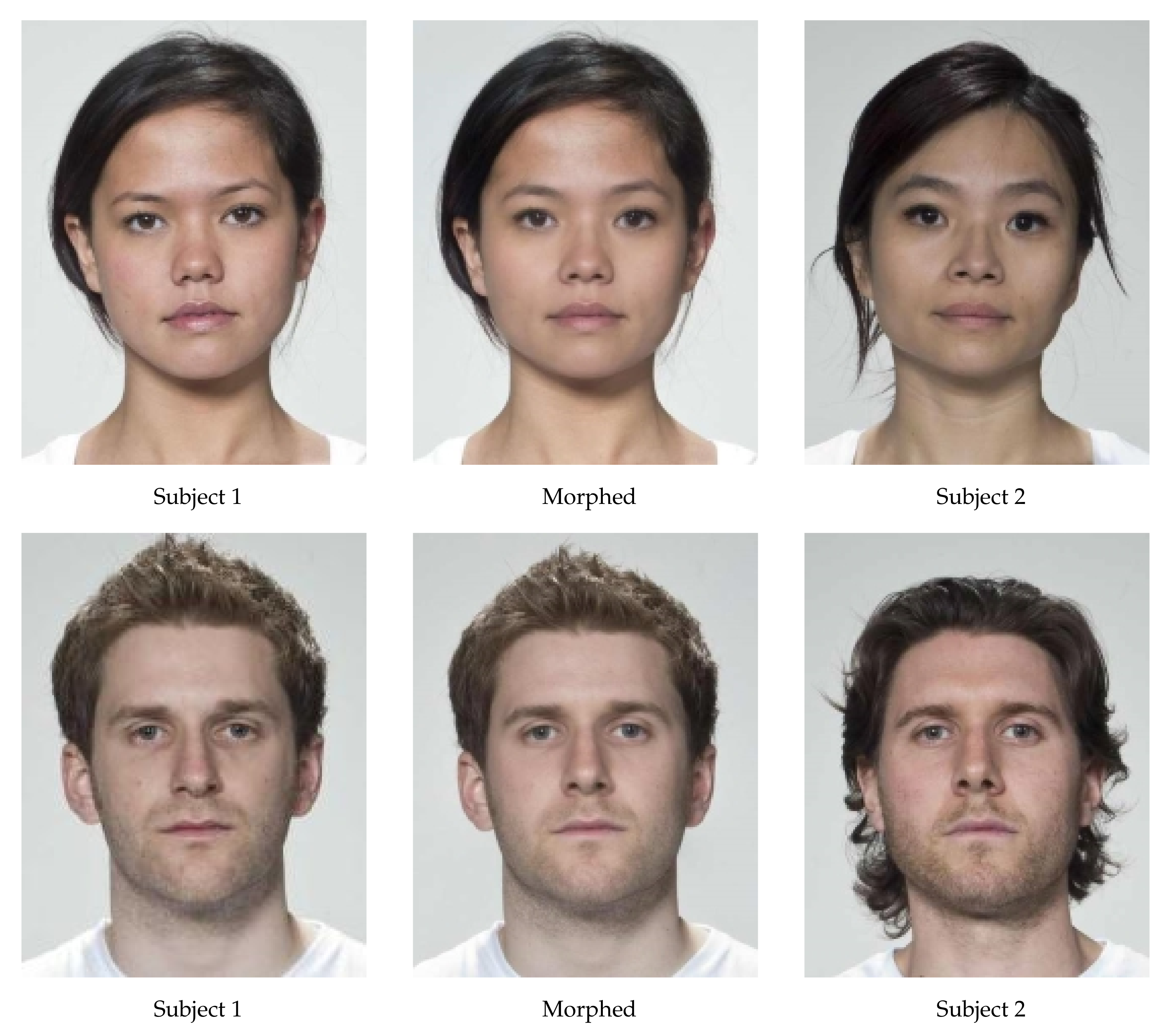










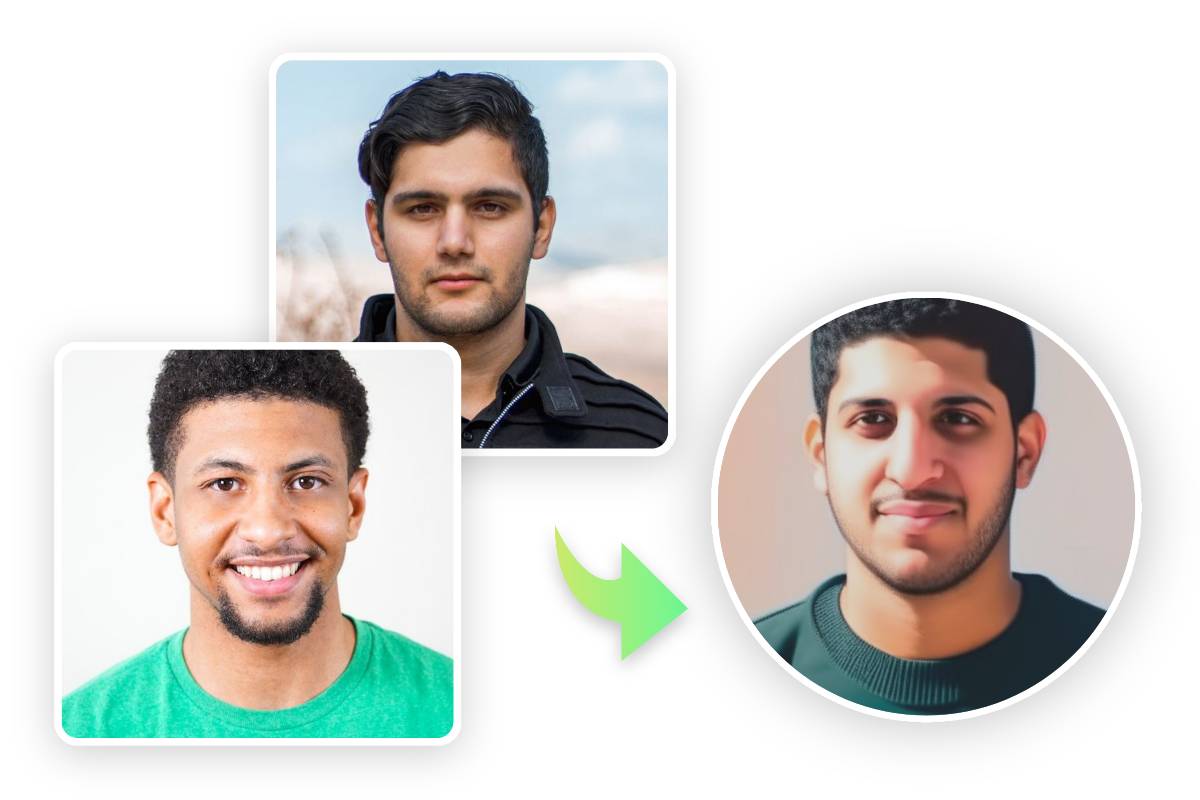
![PDF] Face Recognition Systems Under Morphing Attacks: A Survey | Semantic Scholar PDF] Face Recognition Systems Under Morphing Attacks: A Survey | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/680405eab6adfdeab5aba0e182b6210e6dbe9406/5-Figure5-1.png)